Extracting business lessons from energy sector cyberattacks
Antonio Matamala, Country Manager, Beamex Germany
On December 23, 2015, the first publicly acknowledged successful cyberattack on a power grid occurred. The target was Ukraine, resulting in outages for approximately 230,000 consumers for up to six hours. Since then, the threat of more attacks has only grown, taking us far beyond cyber espionage and stealing business secrets. Cybersecurity is now of extreme importance.
Modern society is built on the energy sector, making it susceptible to intentional harm from state-sponsored groups and malicious actors. As these cyber wars are being fought in the dark, it becomes imperative for all stakeholders to step up and prioritise the security of our energy infrastructure. Together, we must take collective responsibility to fortify our defences.
Mitigating Cybersecurity Risks in SCADA
When reading about the method of attack used in Ukraine, I was not surprised to see that the hackers had seized the SCADA (supervisory control and data acquisition) system. Once SCADA is under your command, you gain complete control over any monitored assets since the software talks with the hardware.
It was once difficult to access a SCADA system because it was a completely isolated system with proprietary protocols. These OT (operational technology) systems were not connected to the corporate network, and a strict wall always separated them from communicating through the Internet. However, this led to technical challenges.
With SCADA at the heart of many operations in the energy and process industries, there has been a growing trend to converge OT with IT since data is essential to drive decision-making processes. The merging of these two fields has opened doors to using AI for a data-driven strategy and predictive maintenance but makes you vulnerable.
With the advent of connectivity through standard Internet protocols, gaining unauthorised access has become alarmingly convenient for hackers. Compounding this issue is numerous outdated legacy systems still in operation. SCADA systems, designed to endure for decades, may typically receive updates only once every ten years, leaving them open to potential cybersecurity breaches.
Addressing this concern requires a concerted effort towards continuous improvement that effectively tackles existing and future threats. More than isolating every aspect of our interconnected infrastructure is needed, thus demanding a proactive approach to identifying and implementing effective countermeasures.
Exposing the Illusion of On-Premises Safety
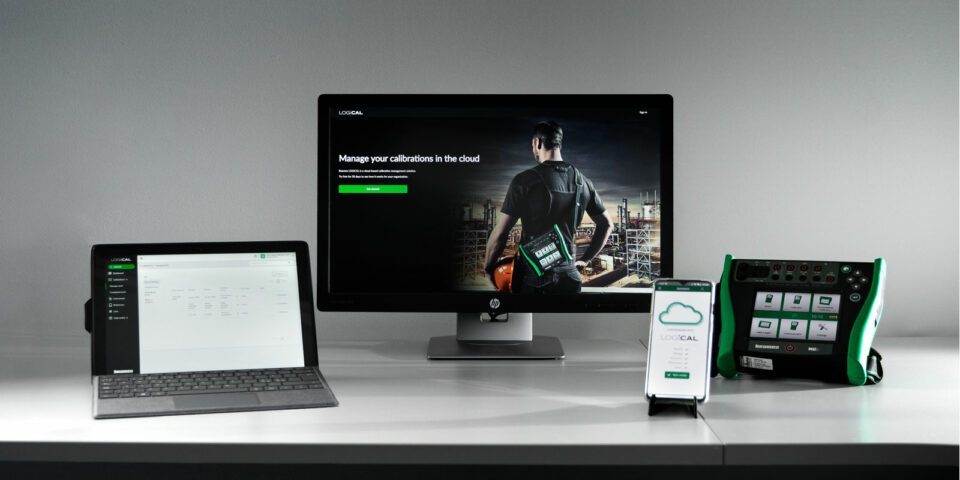
During customer conversations regarding calibration management systems, Beamex discusses different software solutions based on requirements, functional scope, technologies and deployment strategies. It is nothing exceptional to have a more traditional on-premise “desktop” solution and a SaaS (Software as a Service) cloud offering in a company’s solution portfolio, as both address different needs.
However, when we introduce more contemporary approaches such as SaaS, we often encounter resistance from customers who harbour concerns and suspicions about the security and destination of their data. They tend to perceive data hosting by a third party as insecure, favouring on-site hosting software as a safer alternative. But that safety is often an illusion.
A multitude of cyberattacks have occurred in the past year. Notably, even renowned entities like the German automotive giant Continental and the German arms manufacturer Rheinmetall have fallen victim. Who is safe if these industry giants can be hacked?
It exposes the false sense of security and the misguided belief that one can achieve higher protection than industry giants like Amazon and Microsoft, who face relentless attacks throughout the year. Safety is ingrained in their core operations. Attempting to rival the expertise of these seasoned cybersecurity professionals is an insurmountable challenge.
Cloud shaping our tech landscape
Discussions about adopting SaaS platforms can be challenging, mainly when customers already use tools like Microsoft’s Office 365 to manage sensitive data, such as contractual documents, agreements, and payroll information. In comparison, calibration data may be considered less appealing to potential hackers. Still, Beamex’s SaaS solution is underpinned by the same technological infrastructure as Microsoft, so don’t fall into a cognitive bias trap.
Work with trusted partners who take cybersecurity seriously because the consequences can be severe and jeopardise your future. For example, a mid-sized pharma client was hacked over a year ago. They couldn’t do anything for months, and it is doubtful they have recovered all their stolen information. In another case, a company well-known to the author was hacked, and the owner spent weeks reassuring every customer that he would do everything to ensure all would be all right.
In the AI era, the importance of cybersecurity is underscored by personal stories highlighting the severe consequences of cyberattacks. Organisations must prioritise strong cybersecurity measures and proactive risk mitigation to protect against hacking. Leveraging AI becomes crucial as it allows companies to stay ahead in this rapidly evolving digital age. With AI models like ChatGPT demanding significant computing power, shifting to cloud infrastructure becomes necessary. The combination of AI, cloud technologies, and cybersecurity will play a pivotal role in shaping our tech landscape.
You might also find interesting

For a safer and less uncertain world
Welcome to our series of topical articles where we discuss the impact that accurate measurement and calibration has on the world and our everyday lives.